How is TTS evaluation conducted securely?
TTS
Security
Speech AI
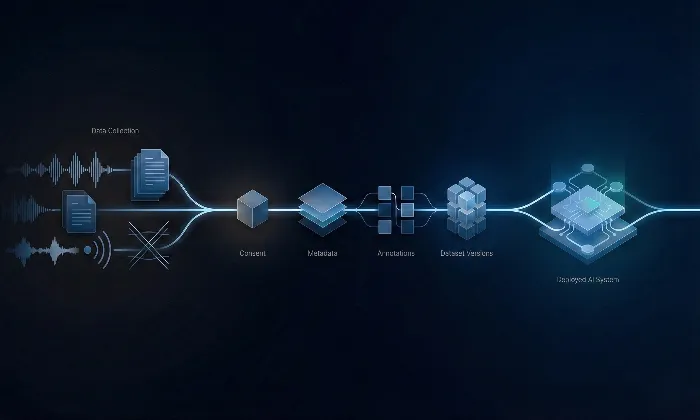
In the rapidly evolving landscape of Text-to-Speech systems, security in evaluation is not just a checkbox. It forms the backbone of trust and operational integrity. Without disciplined security practices, even high-performing TTS models can expose sensitive data, compromise evaluation validity, and erode user confidence. A secure evaluation framework protects data, preserves auditability, and strengthens long-term model reliability.
Imagine a model that performs well in controlled tests but exposes sensitive information because evaluator access was loosely governed. Security failures during evaluation do not stay confined to the lab. They directly affect production trust. A secure framework protects datasets, evaluator workflows, and decision records while ensuring that evaluation insights remain reliable and defensible.
Core Best Practices for Secure TTS Evaluation
Enforce Robust Access Control: Access to evaluation environments must be strictly permission-based. Role-based permissions, multi-factor authentication, and least-privilege data exposure reduce unnecessary risk. Evaluators should only access the specific data required for their assigned tasks. Segmented access prevents accidental or intentional misuse.
Maintain Comprehensive Audit Logging: Every evaluation action should be traceable. Log who accessed which dataset, when evaluations were completed, and under what task configuration. Maintain version control for prompts, scripts, and datasets to prevent ambiguity. Audit trails provide transparency, enable reproducibility, and allow rapid investigation if irregularities arise.
Protect Data Integrity Through Layered Safeguards: Combine encryption, secure storage, controlled download permissions, and restricted exports. Technical controls must be reinforced by procedural safeguards such as periodic audits and compliance checks. Security is strongest when layered, not singular.
Uphold Evaluator Quality and Accountability: Security is not only technical. It includes human discipline. Embed attention checks, monitor evaluator consistency, and retrain or remove low-quality contributors. Reliable evaluation depends on trustworthy human oversight. At FutureBeeAI, evaluator qualification, monitoring, and retraining protocols are integrated into the evaluation lifecycle to preserve integrity.
Strategic Approaches to Secure Evaluation
A secure evaluation system is both preventive and adaptive. It anticipates vulnerabilities before they escalate.
Foster a culture of security awareness among evaluators and stakeholders.
Conduct regular reviews of access permissions and task configurations.
Align security protocols with industry best practices and evolving compliance requirements.
Use purpose-built platforms that support secure workflows for TTS models.
Security must evolve alongside the models themselves. As datasets grow and evaluation complexity increases, governance must scale accordingly.
Conclusion
Secure evaluation is not an administrative overhead. It is a strategic asset. When access control, auditability, and evaluator accountability are embedded into the evaluation process, organizations reduce risk while strengthening model credibility.
By prioritizing structured security frameworks, teams ensure that their TTS systems are not only perceptually refined but also operationally protected. FutureBeeAI supports organizations in building secure, auditable, and scalable evaluation ecosystems that safeguard both data and trust.
What Else Do People Ask?
Related AI Articles
Browse Matching Datasets
Acquiring high-quality AI datasets has never been easier!!!
Get in touch with our AI data expert now!