Why is platform-level security critical for TTS evaluation?
TTS
Security
Speech Applications
Imagine deploying a high-performing Text-to-Speech system that clears every benchmark, only to discover later that evaluation data was compromised. The model did not fail because of architecture limitations. It failed because the evaluation foundation was insecure.
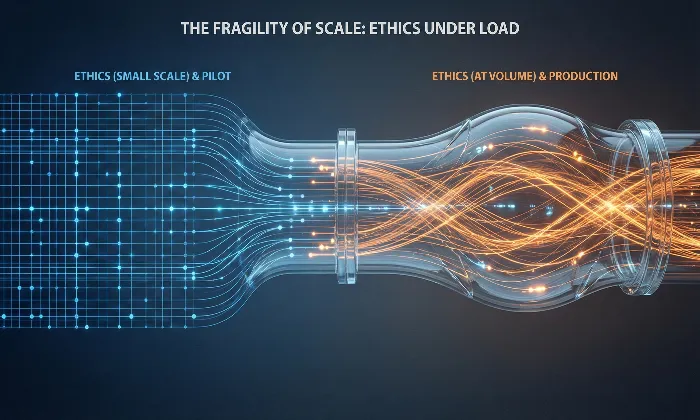
In Text-to-Speech model evaluation, platform-level security protects more than files and dashboards. It safeguards decision quality, dataset authenticity, and long-term model reliability. When evaluation environments are vulnerable, the conclusions drawn from them become unreliable.
How Security Directly Impacts Evaluation Outcomes
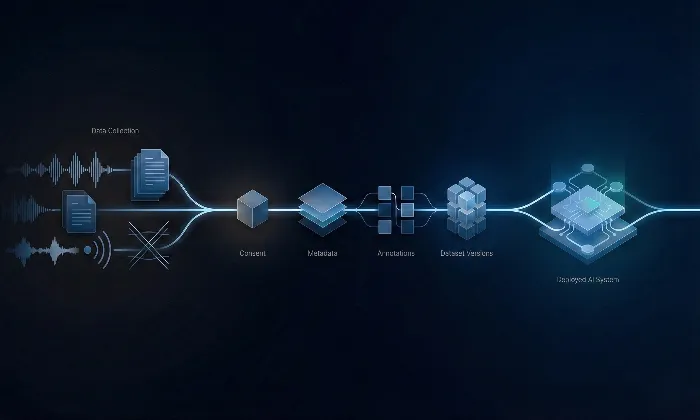
Data Integrity: Evaluation datasets must remain immutable. Unauthorized edits, corrupted uploads, or silent data substitutions can distort performance signals. Encryption, role-based access control, and environment isolation ensure that evaluation data remains unchanged and trustworthy.
Evaluator Trust and Authentic Feedback: When evaluators know that their submissions are securely stored and anonymized where necessary, they provide honest and unbiased feedback. Insecure systems can discourage participation or encourage cautious, diluted responses that weaken evaluation quality. At FutureBeeAI, secure contributor workflows are central to maintaining authentic evaluation inputs.
Regulatory and Compliance Alignment: Industries such as healthcare, finance, and education require strict adherence to data protection frameworks. Evaluation environments must support compliance through access logging, data governance controls, and secure storage standards. Security becomes both a legal and operational necessity.
Auditability and Traceability: Secure platforms maintain comprehensive logs capturing who accessed datasets, who evaluated samples, and what changes were made. These audit trails enable rapid investigation of anomalies, reproducibility of results, and accountability across evaluation cycles.
Protection Against Silent Dataset Drift: Unauthorized modifications or poorly governed version updates can introduce silent performance shifts. Secure dataset versioning ensures that model comparisons remain valid and historically traceable.
Confidence in Iterative Development: Secure systems allow teams to iterate without fear that evaluation results have been compromised. This accelerates improvement cycles while maintaining trust in performance measurements.
Operational Risks of Weak Evaluation Security
Corrupted datasets leading to inflated performance indicators
Manipulated evaluation samples masking regressions
Loss of evaluator confidence and reduced participation quality
Regulatory exposure and reputational damage
Inability to reproduce past results due to missing audit logs
Building a Secure Evaluation Infrastructure
To ensure trustworthy TTS validation, platforms must incorporate:
End-to-end encryption for audio files and feedback data
Strict role-based access controls
Version-controlled datasets with change tracking
Detailed contributor and session metadata logging
Secure storage and regulatory-aligned governance practices
At FutureBeeAI, evaluation workflows are built with layered security architecture, structured access management, and transparent audit mechanisms to preserve data fidelity and decision accuracy.
Practical Takeaway
TTS evaluation security is not peripheral infrastructure. It directly determines whether performance insights are valid.
Without platform-level protection, even the most sophisticated evaluation methodologies risk producing distorted conclusions. Secure environments protect datasets, preserve evaluator trust, and ensure regulatory alignment.
To strengthen your TTS evaluation foundation and protect the integrity of your model development lifecycle, connect with FutureBeeAI and build on a platform designed for secure, reliable AI validation.
What Else Do People Ask?
Related AI Articles
Browse Matching Datasets
Acquiring high-quality AI datasets has never been easier!!!
Get in touch with our AI data expert now!